Billions Of Gmail Accounts Threatened By Stealthy ‘No-Reply’ Hack
What You Can Do to Stay Safe from Hyper-Realistic Phishing
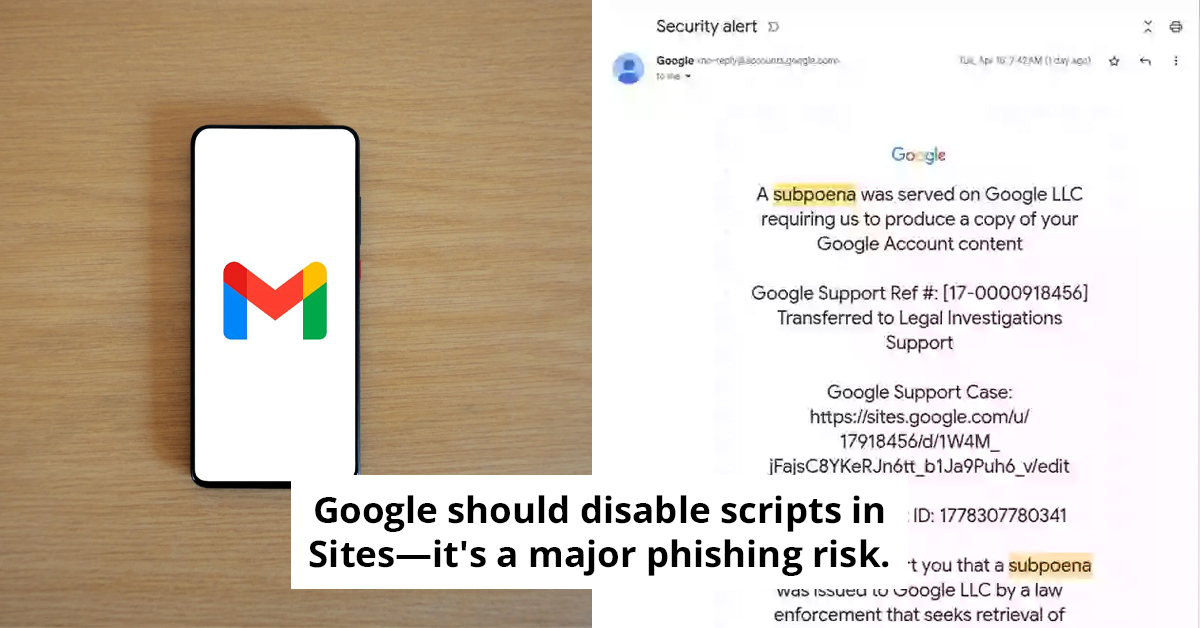
Some people got a “Security Alert” from no-reply@google.com and still felt that tiny, wrong feeling, because the email looked perfect. No obvious typos, no weird sender, no obvious reason to hit delete.
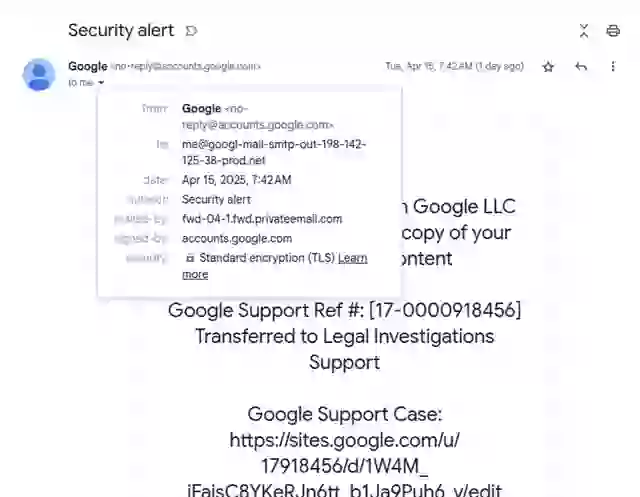
It started when attackers registered a domain and spun up a Gmail account like me@domain.com, then built a Google OAuth app that could trigger Google’s own signed security email. The message sailed through checks with a valid DKIM signature, and then the scammers simply forwarded it to real targets, often tucked inside threads that already contained legitimate Google alerts.
The scariest part is how easy it is to miss, Gmail even shortens the recipient to “me,” like it would for the real thing.
Did you get an email from no-reply@google.com?
So, how do attackers pull off something this slick? According to Johnson, the process is both clever and deeply concerning.
It starts with the scammers registering a domain and setting up a Google account for something like me@domain.com. Next, they create a Google OAuth app, which is usually used to give third-party apps secure access to Google accounts.
But in this case, the scammers use the app to trigger a legitimate Google “Security Alert” email that Google’s system signs and sends itself.
The trick is what happens next: the scammers forward that message to their targets. Because the message is technically still valid, it appears in users’ inboxes without warning signs, often inside threads containing real alerts from Google.
Even the “sent to” field is misleading. Because the attacker named their Google account “me@...,” Gmail displays the recipient as “me,” which is how Gmail typically shortens your address. That subtle touch eliminates another potential tip-off.
 Getty Images
Getty ImagesThe blank space might be a red flag that something’s fishy.
According to Johnson, this phishing campaign relies on two significant gaps in Google’s infrastructure.
First, Google Sites allows users to host content on a Google.com subdomain. There’s no easy way to report abuse directly through the Sites interface, and attackers can quickly change out scripts and embedded content.
Johnson says this alone makes it an ideal staging ground for phishing: “Google should disable scripts and arbitrary embeds in Sites. It’s just too powerful a phishing vector.”But it’s the email’s authenticity that’s the real issue. “The email is much more sophisticated,” Johnson emphasized. The system fails to flag it because of how DKIM works; it checks the message’s headers and content, not the original sending envelope.
 Twitter
Twitter
This email was legitimately sent from no-reply@google.com.
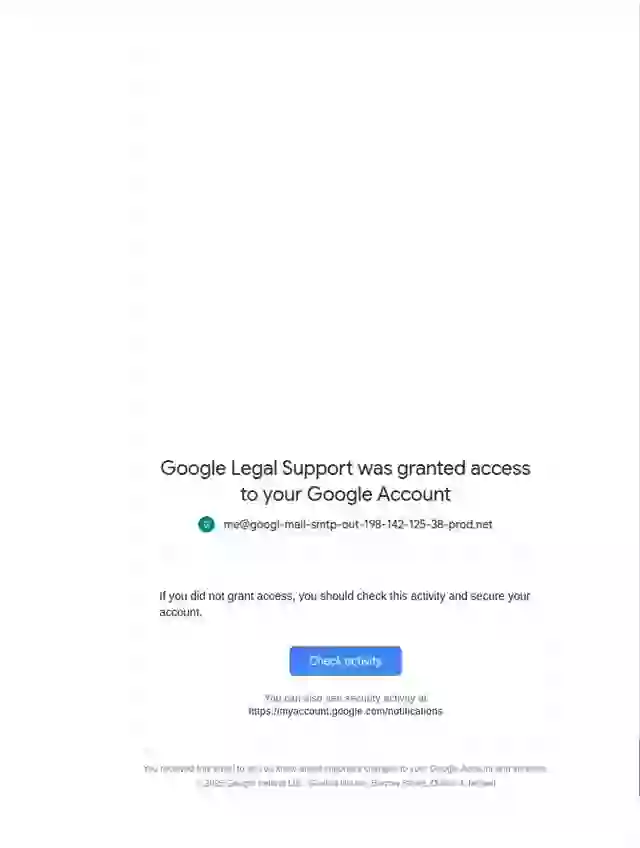
Johnson noticed that while the email appeared to come from Google, it was sent by privateemail.com. Also, buried in a block of space was a second, odd-looking message: “Google Legal Support was granted access to your Google Account.”
That line, paired with the repeated use of the strange me@... address, was another red flag. Johnson reported the issue to Google, which later responded that it plans to fix the OAuth loophole.
 Twitter
Twitter
That’s why the inbox surprise hits so hard, the email arrives as if it came from Google’s own system, complete with the same kind of thread users already trust.
Then the trick gets sneakier, because the attacker’s “me@...” setup makes the “sent to” display look totally normal, even when the target never signed up for anything.
Cybersecurity expert Eugene Kaspersky emphasizes that phishing scams have evolved to exploit trust and familiarity. Modern attacks often mimic legitimate communications, using sophisticated designs and personalized messages to trick victims.
He suggests that individuals should verify email headers and URLs before clicking any links. Kaspersky recommends using a multi-layered security approach, including spam filters and antivirus software, to help identify potential threats before they reach the inbox.
Additionally, he advocates for regular education on recognizing phishing attempts as essential for personal and organizational cybersecurity.
Speaking of hidden threats, Harvard-affiliated researchers say the odd evidence may point to Earth-based intelligence, not visitors from another world.
Next comes the staging ground, attackers can host and swap phishing content on Google Sites under a Google.com subdomain, with little friction to report or shut it down.
Strong communication skills can significantly reduce vulnerability to phishing scams.
This phishing email is alarmingly well-crafted.
A Google spokesperson acknowledged the threat, saying:
“We’re aware of this class of targeted attack from this threat actor and have rolled out protections to shut down this avenue for abuse. In the meantime, we encourage users to adopt two-factor authentication and passkeys, which provide strong protection against these kinds of phishing campaigns.”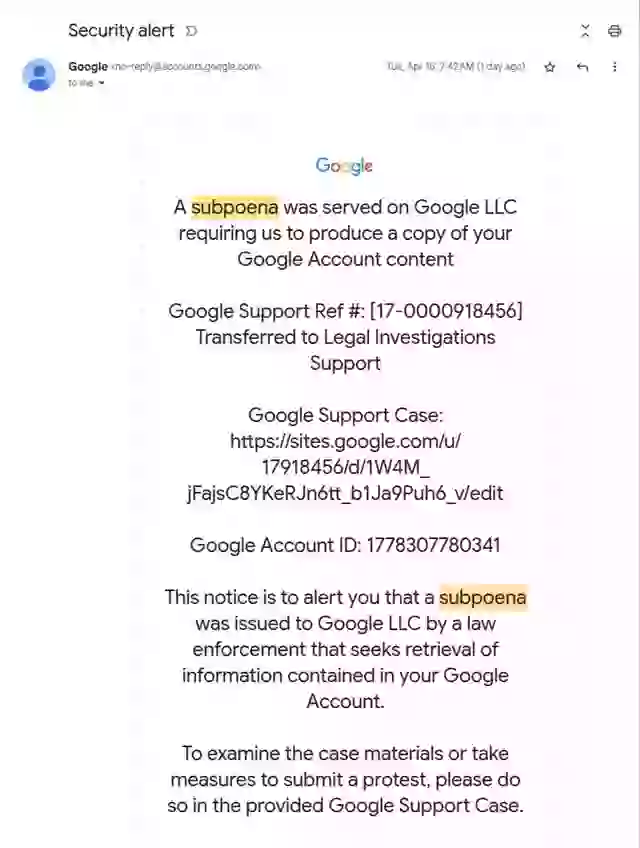 Twitter
Twitter
And that’s the punchline, the real failure isn’t the email format, it’s how the whole chain slips past flags because it is technically still valid.
This attack didn’t rely on technical errors or user laziness. It exploited official systems, appeared in familiar inbox threads, and came from real domains, making it dangerous.
While Google is working on a fix, staying alert is the safest approach right now. Look closely at email addresses, double-check domains, and when in doubt, don’t click. Even a tiny detail can make all the difference.
As phishing scams become more sophisticated, the need for vigilance in protecting personal information has never been more critical. The article highlights how modern phishing attempts have shed their amateurish appearances, making them harder to identify even for experienced users. This evolution underscores the importance of ongoing education about these emerging threats.
To combat this wave of stealthy attacks, individuals and organizations should prioritize regular training sessions to boost awareness and preparedness. Implementing practical strategies like multi-factor authentication and secure password management can significantly mitigate the risks associated with these cunning scams. Ultimately, a well-informed user stands as the first line of defense in the ever-evolving landscape of cybersecurity.
Now you’re left wondering whether the “Security Alert” was a warning or the bait.
At first glance, water seems simple, but read how researchers mapped the hidden mega mass beneath the equator in Atlantic researchers reveal the water beneath the equator.